
Keep Calm and Simplify Managing your SIEM events with Siemplify
May 9, 2021

We created our Logz.io Cloud-Based SIEM with a clear goal: providing a rapidly deploying, flexible, and cost-effect security management tool that can serve broad datasets and withstand the occasional bursts of events without a sweat. However, our users were coming back to us with requests for more. After all, it’s great to proactively detect proliferating security threats, but what’s the next step beyond just identifying the threat?
There was a clear need to provide a means to respond to these alerts and triggered incidents, and after examining the options at hand, we decided to augment our users with a purpose-built SOAR solution with native integration to our Cloud SIEM.
We were going to have a truly end-to-end solution:
Ingestion → Enrichment → Detection → Investigation → Response

We partnered with Siemplify, one of the leading independent providers of Security Orchestration, Automation and Response (SOAR), to bring that extra response component into our operations.
SIEM and SOAR Together
This new integration with their SOAR tool will let you direct all detections by Logz.io Cloud SIEM straight into the Siemplify platform.
There, pre-defined playbooks will trigger the appropriate steps to investigate (and even remediate) those incidents with the level of automation you feel comfortable with.
In fact, it’s so simplified we even created this 1 minute video of highlights to save you a longer read:
This collaboration is meant to enable SOC (Security Operations Center) engineers and Security analysts to offload mundane tasks into automated workflows which will be based on the type of the events detected.
SOC Events
Each event type (will it be Access event, Threat event or Audit) can be mapped to a certain type of alert on the Cloud SIEM end, where relevant data (e.g. Indicators of Compromise) will be aggregated and carried inside the alert over to Simplify’s SOAR platform.
At that point, the triggered alert will be translated as a new security incident of a type mapped to the original alert’s type.
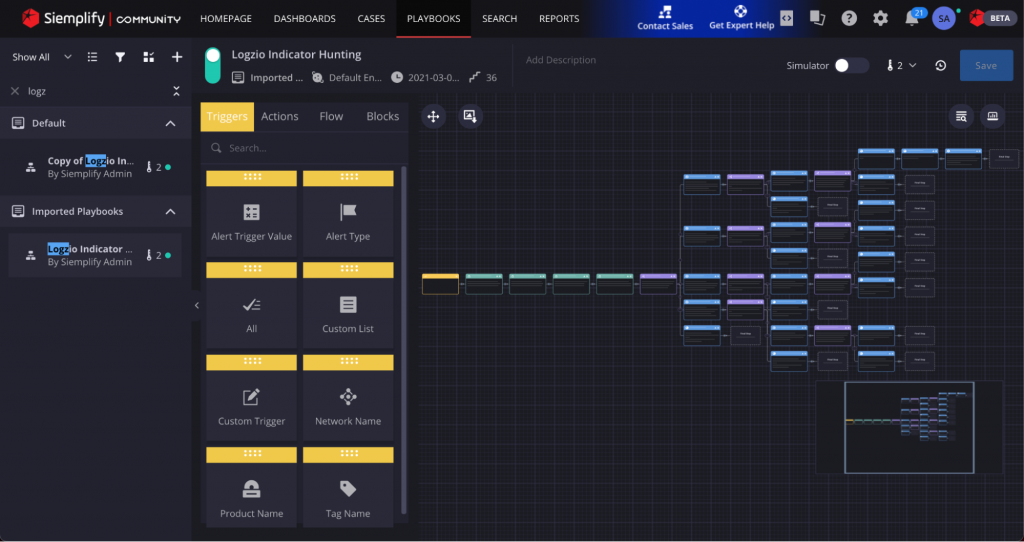
Playbooks
A predefined playbook, which is mapped to this incident type, will be triggered, executing the investigative actions set in the playbook while collaborating the relevant team members with the findings and outcomes.
The playbooks can cover a wide range of activities such as continuous querying of the Cloud SIEM for additional information, further enrichment of the data retrieved from the logs, triaging, exposing relations and correlations between entities and executing remediation actions such as blocking access for a certain range of IPs.
This entire flow can be either fully automated or include checkpoints where human intervention will be summoned.

The elasticity of the Cloud SIEM data parsing and analytics, accompanied by the ability Siemplify offers to translate a documented workflow into an actionable playbook – will offload many of the manual tasks into automation, that will save you man-hours, reduce your Incidence Respond spend, and keep your team away from experiencing alert-fatigue and burnout.
For information on how to set up this integration, please refer to this article.
Logz.io’s Security Analysts will keep contributing additional playbooks as we gather feedback on desired use -cases that our mutual users can benefit from. Have an idea? Drop us a line with your suggestion in our community channel, or contact your designated customer success engineer (if you’re a customer).


